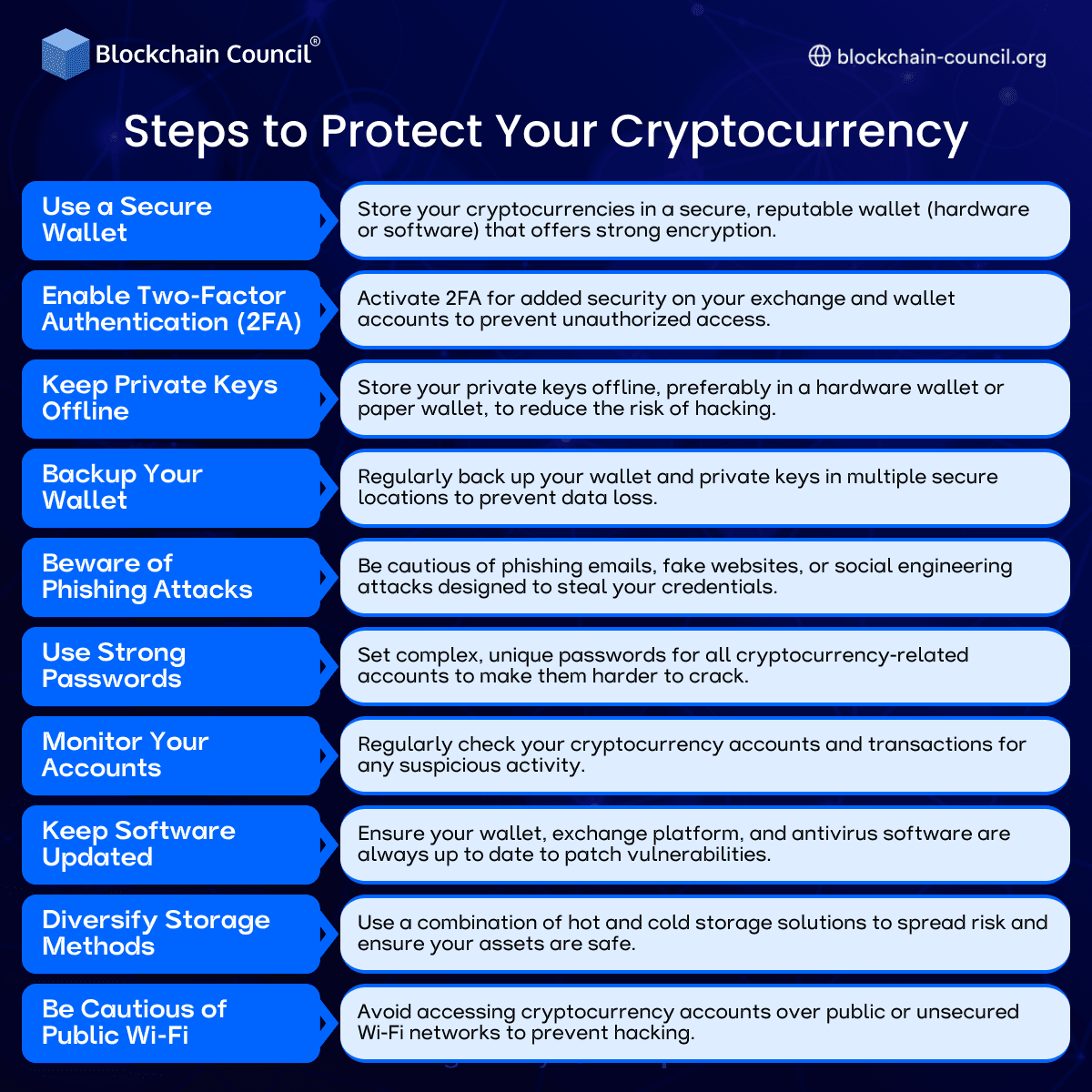
Steps to Protect Your Cryptocurrency
Cryptocurrency offers financial freedom, decentralization, and global accessibility. It also comes with one uncomfortable truth: if you lose access or get hacked, there is usually no customer support to rescue you. That makes security not optional, but essential.
To build a solid understanding of crypto security and blockchain fundamentals, many professionals begin with structured programs such as the Cryptocurrency Expert Certification and the AI expert certification. These certifications provide a strong foundation in both digital assets and emerging technologies that intersect with security practices.

This article explains the most effective steps to protect your cryptocurrency, recent developments in crypto security, and practical strategies you can apply immediately.
Why Cryptocurrency Security Matters
Unlike traditional banking systems, cryptocurrency transactions are irreversible. Once funds are sent, they cannot be recovered. There is no central authority to reverse fraud or restore access.
Common risks include:
Phishing attacks
Exchange hacks
Lost private keys
Malware and ransomware
Even experienced investors have lost millions due to basic security mistakes. That should tell you how unforgiving this space can be.
1. Use a Secure Cryptocurrency Wallet
The first step in protecting your crypto is choosing the right wallet.
Types of Wallets
Hardware wallets
Software wallets
Mobile wallets
Web wallets
Best Practice
Hardware wallets are considered the most secure because they store private keys offline.
Example
Devices like Ledger and Trezor keep your assets isolated from internet-based threats, reducing the risk of hacking.
2. Enable Two Factor Authentication
Two factor authentication adds an extra layer of security to your accounts.
How It Works
In addition to your password, you must verify your identity using a second factor such as a mobile app or code.
Why It Matters
Even if someone gets your password, they cannot access your account without the second factor.
Tip
Use authentication apps instead of SMS-based verification for better security.
3. Keep Your Private Keys Offline
Your private key is the only way to access your cryptocurrency. If someone gets it, your funds are gone.
Best Practice
Store private keys offline using:
Hardware wallets
Paper backups
Example
Many investors use cold storage methods to keep large amounts of crypto safe from online threats.
4. Regularly Backup Your Wallet
Losing access to your wallet can be just as damaging as getting hacked.
Backup Methods
Secure physical copies
Encrypted digital backups
Best Practice
Store backups in multiple secure locations to prevent loss due to damage or theft.
5. Beware of Phishing Attacks
Phishing is one of the most common ways people lose cryptocurrency.
Common Tactics
Fake emails
Fake websites
Social engineering
Example
A user receives an email that looks like it is from a crypto exchange and enters login details on a fake website.
Prevention
Always verify URLs and avoid clicking suspicious links.
6. Use Strong and Unique Passwords
Weak passwords are an open invitation for attackers.
Best Practice
Use long, complex passwords
Avoid reusing passwords across platforms
Tools
Password managers can help generate and store secure passwords.
7. Monitor Your Accounts Regularly
Regular monitoring helps detect suspicious activity early.
What to Check
Transaction history
Login attempts
Account settings
Example
Unexpected withdrawals or login alerts can indicate a security breach.
8. Keep Software and Devices Updated
Outdated software often contains vulnerabilities.
Best Practice
Update wallets and apps regularly
Use updated antivirus software
Example
Security patches fix known vulnerabilities that hackers exploit.
9. Diversify Storage Methods
Do not keep all your crypto in one place.
Strategy
Use both hot wallets and cold wallets
Spread assets across multiple platforms
Benefit
Even if one wallet is compromised, your entire portfolio is not at risk.
10. Avoid Public WiFi for Transactions
Public networks are often insecure and can expose your data.
Risk
Hackers can intercept data on unsecured networks.
Best Practice
Use secure, private connections or VPNs when accessing crypto accounts.
Role of AI in Cryptocurrency Security
AI is increasingly being used to enhance crypto security.
Applications
Fraud detection
Transaction monitoring
Threat analysis
Example
AI systems can detect unusual transaction patterns and flag potential fraud in real time.
Professionals interested in building such systems often explore programs like the AI Powered coding expert Course, which focuses on practical AI applications.
Marketing and Security Awareness
Security awareness is also part of user education and communication strategies. Programs like the AI powered marketing course help organizations educate users effectively about risks and best practices.
Because apparently, people only take security seriously after losing money, which is not the ideal learning method.
Recent Developments in Crypto Security
Multi Signature Wallets
These require multiple approvals for transactions, adding an extra layer of security.
Biometric Authentication
Some platforms now use fingerprint or facial recognition for access.
Decentralized Identity Systems
These reduce reliance on centralized authentication methods.
AI Driven Threat Detection
AI is improving the speed and accuracy of identifying cyber threats.
Common Mistakes to Avoid
Sharing private keys
Using unsecured devices
Ignoring software updates
Falling for scams
These mistakes are surprisingly common and entirely preventable.
Best Practices Summary
Use hardware wallets
Enable two factor authentication
Keep private keys offline
Monitor accounts regularly
Stay informed about threats
Security is not a one-time setup. It is an ongoing process.
Future of Cryptocurrency Security
The future includes:
More advanced AI security systems
Improved encryption methods
Greater user awareness
As crypto adoption grows, security will become even more critical.
Conclusion
Protecting your cryptocurrency requires a combination of technology, awareness, and discipline. From securing wallets to avoiding phishing attacks, every step plays a role in safeguarding your assets.
While the technology continues to evolve, the fundamental principle remains the same: control your keys, control your crypto. Ignore that, and the market will teach you the hard way.
FAQs
1. What is the safest way to store cryptocurrency
The safest way to store cryptocurrency is using a hardware wallet that keeps private keys offline and away from internet threats. This method significantly reduces the risk of hacking compared to online storage. Combining hardware wallets with proper backups further enhances security.
2. Why is two factor authentication important
Two factor authentication adds an extra layer of security by requiring a second verification step beyond a password. This makes it much harder for unauthorized users to access your account. It is one of the simplest yet most effective security measures.
3. What are private keys
Private keys are cryptographic codes that allow access to your cryptocurrency. They must be kept secure and never shared with anyone. Losing them means losing access to your funds permanently.
4. How can I avoid phishing attacks
You can avoid phishing attacks by verifying website URLs, avoiding suspicious links, and not sharing personal information. Always double check emails and messages claiming to be from exchanges. Awareness is key to prevention.
5. What is a hardware wallet
A hardware wallet is a physical device that stores private keys offline. It provides a high level of security against online threats. These wallets are widely used by serious investors.
6. How often should I backup my wallet
You should backup your wallet whenever you make significant changes or updates. Regular backups ensure you can recover access if needed. Storing backups securely is equally important.
7. Can cryptocurrency be hacked
Cryptocurrency itself is secure, but wallets and exchanges can be hacked if not properly protected. Most breaches occur due to user errors or weak security practices. Proper precautions can minimize risks.
8. What is cold storage
Cold storage refers to keeping cryptocurrency offline, away from internet access. This method is highly secure and commonly used for long term storage. It protects assets from online threats.
9. Why should I avoid public WiFi
Public WiFi networks are often unsecured and can expose your data to hackers. Using them for crypto transactions increases the risk of interception. It is safer to use private or secure networks.
10. What is multi signature security
Multi signature security requires multiple approvals for a transaction, adding an extra layer of protection. It reduces the risk of unauthorized access. This method is often used by organizations.
11. How do strong passwords help
Strong passwords make it harder for attackers to guess or crack your credentials. Using unique passwords for each account further improves security. Password managers can assist in managing them.
12. What role does AI play in crypto security
AI helps detect unusual patterns and potential threats in real time. It enhances fraud detection and monitoring systems. This improves overall security in the crypto ecosystem.
13. What happens if I lose my private key
If you lose your private key, you lose access to your cryptocurrency permanently. There is no recovery mechanism. This highlights the importance of secure storage and backups.
14. Are exchanges safe for storing crypto
Exchanges offer convenience but are not the safest option for long term storage. They can be vulnerable to hacks. It is recommended to use personal wallets for better security.
15. How can beginners secure their crypto
Beginners should start by using secure wallets, enabling two factor authentication, and learning basic security practices. Education is essential for avoiding common mistakes. Taking small steps can make a big difference.
16. What is a phishing website
A phishing website is a fake site designed to look like a legitimate platform to steal user information. It tricks users into entering login credentials. Always verify URLs before logging in.
17. How does diversification improve security
Diversifying storage reduces risk by spreading assets across multiple wallets or platforms. If one is compromised, others remain safe. This strategy improves overall protection.
18. What are common crypto scams
Common scams include phishing emails, fake investment schemes, and impersonation attacks. These scams aim to steal funds or sensitive information. Awareness helps in avoiding them.
19. Is cryptocurrency safe for long term investment
Cryptocurrency can be safe for long term investment if proper security measures are followed. Risks can be minimized with careful management. Security practices are essential for protecting assets.
20. Why is crypto security important
Crypto security is important because there is no central authority to recover lost or stolen funds. Users are responsible for protecting their assets. Proper security ensures long term safety and peace of mind.
Related Articles
View All
Infographics
Cryptocurrency Regulations Comparison: A Global Overview
Explore how different countries regulate cryptocurrencies, from strict compliance frameworks to evolving policies. This guide breaks down key differences in taxation, legality, and regulatory approaches worldwide.

Infographics
Steps To Develop Hyperledger Solution On Cloud Service
Hyperledger is uniting the industry to drive an initiative forward and is paramount to the success of distributed ledger technology.

Infographics
Steps To Audit Smart Contracts
Smart Contacts work together with the blockchain technology and automatically generates to its full potential. Learn How to Develop and Audit Smart Contracts.
Trending Articles

The Role of Blockchain in Ethical AI Development
How blockchain technology is being used to promote transparency and accountability in artificial intelligence systems.
AWS Career Roadmap
A step-by-step guide to building a successful career in Amazon Web Services cloud computing.

Top 5 DeFi Platforms
Explore the leading decentralized finance platforms and what makes each one unique in the evolving DeFi landscape.