Blockchain as a Cybersecurity Infrastructure

Blockchain as Cybersecurity
- Blockchain technology provides a tamper-proof security layer by distributing data across multiple independent nodes.
- Distributed ledgers protect logs, identity systems, and audit trails from unauthorized changes.
- Enterprises and governments use blockchain to strengthen cybersecurity, transparency, and compliance.
- Blockchain Council offers training and certifications for implementing blockchain-based security infrastructures.
Introduction
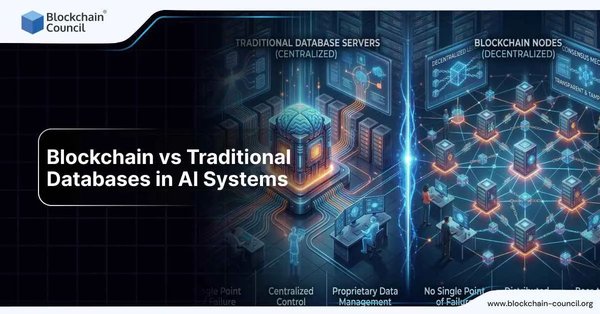
Modern cybersecurity systems rely heavily on centralized databases, creating attractive targets for attackers.
Once compromised, centralized systems allow attackers to alter logs, identities, and audit records silently.
Blockchain technology changes this model by distributing trust across many nodes.
As a cybersecurity infrastructure, blockchain ensures data integrity, transparency, and resistance to tampering.
Security professionals can learn these implementations through Blockchain Council certifications and courses.
Blockchain and Tamper-Proof Security
A. Immutable Distributed Ledgers
Distributed ledgers store identical copies of data across multiple network participants.
No single authority controls the ledger, reducing centralized failure risks.

1. Mechanism of Immutability
Each transaction is grouped into blocks linked using cryptographic hashes.
Altering one record changes the hash, immediately exposing unauthorized modifications.
Consensus mechanisms require network agreement before data becomes permanent.
Benefits for Cybersecurity
- Prevents attackers from secretly modifying security logs.
- Ensures forensic evidence remains accurate during investigations.
- Strengthens trust in shared security data across organizations.
B. Secure Logging and Audit Trails
Traditional logs can be deleted or altered after breaches.
Blockchain-based logs remain permanent, verifiable, and time-stamped.
1. Use Cases
- Government agencies track system access with immutable records.
- Enterprises monitor administrative actions for insider threat detection.
- Regulators verify compliance using transparent audit trails.
Implementation Strategies
- Blockchain records hashes of logs instead of raw data.
- Smart contracts automate log validation and storage.
- Security teams gain expertise through Blockchain Council training programs.
Blockchain for Identity and Access Management
A. Decentralized Identity Systems
Centralized identity providers create single points of failure.
A breach exposes millions of credentials simultaneously.
Decentralized identity systems distribute identity control using blockchain.
1. Advantages of Decentralized Identity
- Users control identity credentials instead of centralized authorities.
- Attackers cannot compromise all identities through one breach.
- Privacy improves through selective disclosure of credentials.
Enterprise Implementation
- Identity credentials are encrypted and anchored on blockchain ledgers.
- Access decisions use cryptographic proofs rather than passwords.
- Professionals learn implementation methods via Blockchain Council certifications.
B. Blockchain-Based Access Controls
Every access request is logged immutably on the blockchain.
Unauthorized access attempts become immediately traceable.
Security Benefits
- Creates accountability for every authentication event.
- Detects abnormal access patterns faster.
- Supports compliance audits with tamper-proof records.
Enterprise and Government Security Applications
A. Enterprise Use Cases
- Secures financial records against manipulation.
- Protects intellectual property logs from insider threats.
- Improves trust between partners sharing sensitive data.
B. Government Use Cases
- Secures citizen identity systems from alteration.
- Protects land registries and healthcare records.
- Enables transparent inter-agency data sharing.
Deployment Considerations
Organizations must choose permissioned blockchains for controlled environments.
Security audits ensure smart contracts behave as intended.
Teams benefit from Blockchain Council courses focused on secure deployments.
Conclusion
Blockchain technology strengthens cybersecurity by creating tamper-proof security infrastructures.
It protects logs, identities, and audit trails from unauthorized modification.
Enterprises and governments gain transparency, resilience, and trust through distributed ledgers.
Professionals can master these systems through Blockchain Council training and certifications.
Adopting blockchain as cybersecurity infrastructure prepares organizations for future digital threats.