Threat Modeling for Blockchain Systems: A Cybersecurity Framework for Secure Distributed Applications
Summary:
- Threat modeling identifies security risks before blockchain systems are deployed.
- Blockchain systems introduce unique attack surfaces across multiple technical layers.
- Structured cybersecurity frameworks improve prevention, detection, and mitigation strategies.
- Effective threat modeling strengthens secure distributed application design.
- Blockchain Council provides training and certifications on blockchain threat modeling practices.
Introduction
Blockchain systems power financial, identity, and enterprise applications globally.
Security failures can result in irreversible losses.
Traditional cybersecurity models do not fully address decentralized environments.
Threat modeling provides a proactive security approach.
It identifies weaknesses before attackers exploit them.
Professionals learn blockchain-focused threat modeling through Blockchain Council courses and certifications.
Understanding Threat Modeling
A. What Is Threat Modeling?
Threat modeling is a structured method for identifying potential security threats.
It evaluates how attackers might exploit system weaknesses.
Purpose of Threat Modeling
The goal is reducing risk through early detection.
It supports secure design decisions.
Core Threat Modeling Objectives
- Identify assets requiring protection.
- Understand attacker motivations.
- Prioritize security risks.
- Define mitigation strategies.
B. Why Blockchain Requires Specialized Threat Modeling
Blockchain systems differ from traditional centralized systems.
They rely on distributed trust and consensus mechanisms.
Unique Blockchain Security Characteristics
- Decentralized network communication.
- Immutable transaction records.
- Publicly visible smart contracts.
Security Implications
These characteristics create new attack vectors.
Generic threat models fail to capture blockchain-specific risks.
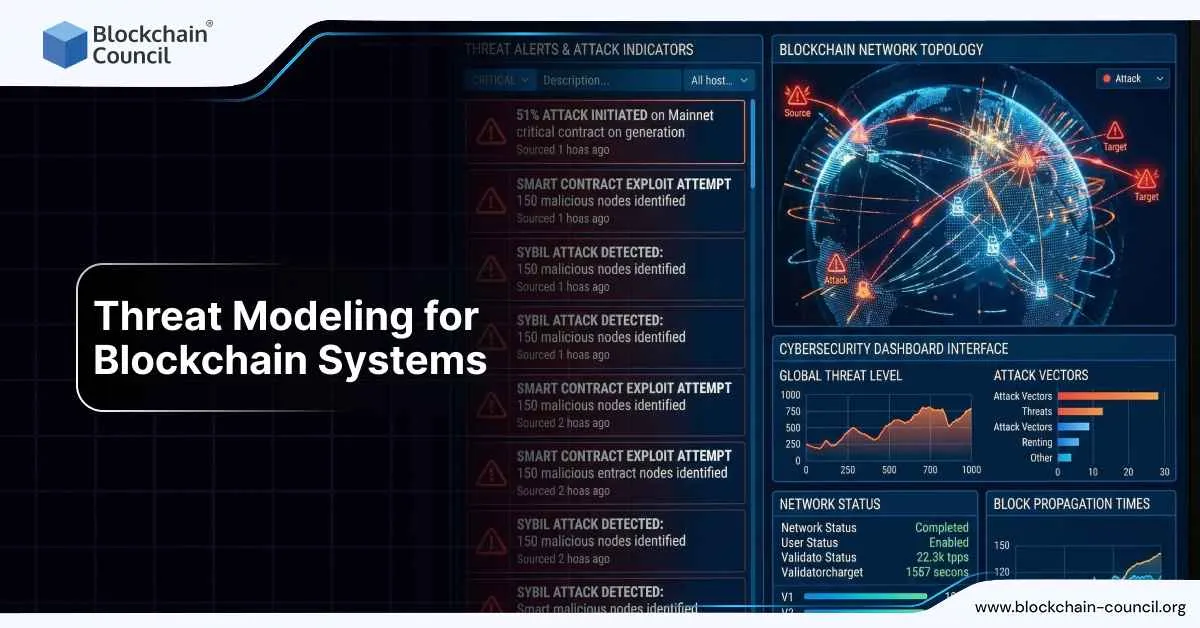
Blockchain Threat Modeling Layers
A. Network Layer Threats
The network layer enables node communication.
Attackers often target this layer first.
Common Network Attacks
- Distributed denial-of-service attacks.
- Eclipse attacks on nodes.
- Traffic interception.
Mitigation Strategies
- Network monitoring.
- Peer diversity enforcement.
- Rate limiting controls.
B. Consensus Layer Threats
Consensus ensures agreement across blockchain participants.
Compromising consensus threatens system integrity.
Consensus Attack Scenarios
- Majority control attacks.
- Validator collusion.
- Consensus manipulation.
Security Controls
- Decentralized validator distribution.
- Slashing mechanisms.
- Continuous consensus monitoring.
C. Smart Contract Layer Threats
Smart contracts automate blockchain logic.
Errors become permanent once deployed.
Common Smart Contract Risks
- Logic flaws.
- Reentrancy vulnerabilities.
- Access control failures.
Prevention Techniques
- Secure coding standards.
- Mandatory audits.
- Formal verification methods.
D. Application Layer Threats
Applications connect users to blockchain systems.
They often represent the weakest security point.
Application-Level Risks
- Poor authentication mechanisms.
- Insecure APIs.
- Phishing integrations.
Mitigation Approaches
- Strong identity controls.
- Secure user interfaces.
- Continuous security testing.
Threat Identification and Assessment
A. Identifying Blockchain Threats
Threat identification requires mapping system architecture.
Assets, trust boundaries, and data flows must be documented.
Identification Techniques
- Architectural diagram analysis.
- Attack surface mapping.
- Historical breach review. Threat Categorization
Threats are grouped by layer and impact severity.
This improves prioritization accuracy.
B. Assessing Threat Impact and Likelihood
Not all threats carry equal risk.
Assessment determines mitigation priority.
Risk Evaluation Factors
- Attack complexity.
- Potential damage.
- Exploit likelihood.
Risk Scoring
Structured scoring supports consistent cybersecurity framework decisions.
Threat Mitigation Strategies
A. Designing Secure Blockchain Architectures
Mitigation begins at the design stage.
Security controls must be embedded early.
Architectural Mitigations
- Defense-in-depth controls.
- Secure key management.
- Role-based access enforcement.
Governance Integration
Governance ensures mitigation controls remain enforceable.
Teams learn governance implementation through Blockchain Council certifications.
B. Continuous Threat Monitoring
Threat modeling is not a one-time exercise.
Blockchain systems evolve constantly.
Ongoing Security Practices
- Continuous monitoring.
- Periodic threat model updates.
- Incident response testing.
Operational Benefits
Continuous threat modeling reduces breach impact significantly.
Benefits of Blockchain Threat Modeling
A. Security and Business Advantages
Threat modeling improves both security and trust.
Organizations gain confidence in deployment decisions.
Key Benefits
- Reduced attack surface.
- Faster incident response.
- Improved stakeholder trust.
Regulatory Support
Structured threat modeling supports regulatory compliance efforts.
Conclusion
Threat modeling is essential for secure blockchain systems.
It addresses risks across network, consensus, smart contract, and application layers.
A structured cybersecurity framework strengthens distributed application security.
Organizations reduce risk through proactive design and monitoring.
Professionals master blockchain threat modeling via Blockchain Council training and certifications.